What Is a Computer Network? Types, Components, and How They Work
This guide covers: What Is a Computer Network? Types, Components, and How They Work.
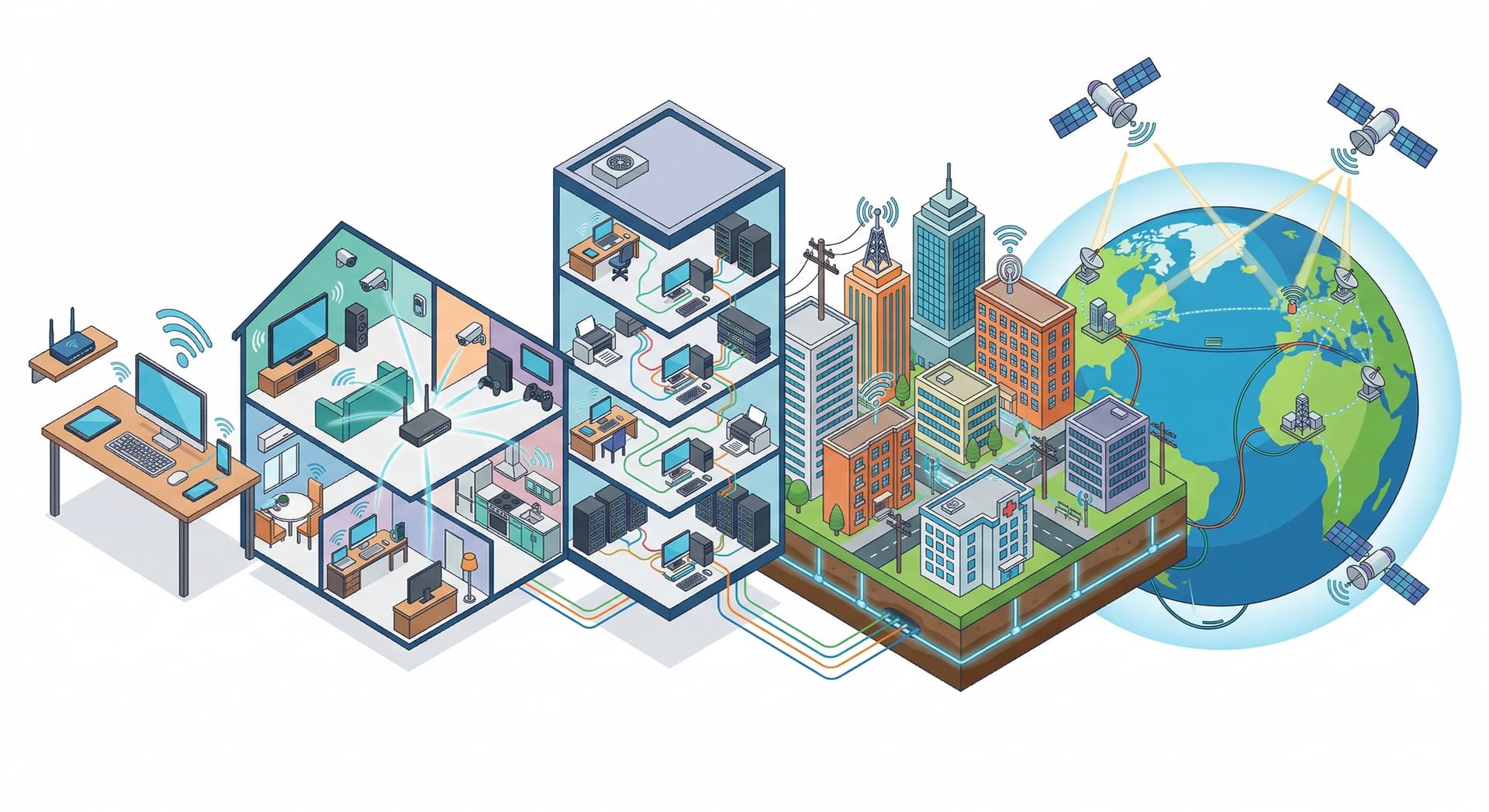
A computer network is a group of devices — computers, phones, printers, servers, and anything else with a network interface — connected so they can exchange data and share resources. Every time you load a webpage, send a message, or print a document from across the room, a computer network makes it happen.
A Brief History
Modern computer networking traces back to ARPANET, a U.S. Defense Department research project launched in the late 1960s. ARPANET introduced packet switching — breaking data into small chunks, routing them independently, and reassembling them at the destination. That concept became the foundation of the internet we use today.
Before networking, every device operated in isolation. If an office had ten computers and each needed to print, the office needed ten printers. Networking changed that equation entirely — connect the devices, share the resources, and suddenly one printer serves the whole floor.
Today, networking extends far beyond office printers. Cloud storage, video streaming, online shopping, email, and smart home devices all depend on the same fundamental idea: devices communicating over a shared network.
How Computer Networks Work
At the most basic level, a network lets devices send data to each other. That data travels in small units called packets. Each packet contains the payload (the actual information) plus header metadata that tells networking equipment where it came from and where it needs to go.
Routers and switches are the traffic controllers. Switches move packets between devices on the same local network. Routers connect separate networks and decide the best path for each packet to reach its destination. When you type a URL into your browser, your device sends a packet request through these devices, across potentially dozens of network hops, to a web server that returns the page you see — usually within milliseconds.
The rules governing how all of this works are called protocols. Protocols define how devices find each other, how they format messages, how they handle errors, and how they keep communication secure. Without standardized protocols, devices from different manufacturers could never talk to each other.
Types of Computer Networks
Networks are categorized primarily by the area they cover. From smallest to largest:
Personal Area Network (PAN)
A PAN connects devices used by a single person within a very small area — typically a few meters. Your phone connecting to wireless earbuds via Bluetooth, or your laptop syncing with a smartwatch, is a PAN. These networks are simple, low-power, and personal by definition.
Local Area Network (LAN)
A local area network connects devices within a single building or small campus — a home, an office, or a school. LANs typically use Ethernet cables or WiFi and offer the highest speeds of any network type because distances are short and the network is privately managed.
Most home networks are LANs. Your router connects your devices to each other and to the internet. Within the LAN, devices can share files, printers, and media without any data leaving your home.
Wireless Local Area Network (WLAN)
A WLAN is simply a LAN that uses radio waves instead of cables. WiFi is the most common WLAN technology. Modern WiFi 6 routers can support dozens of simultaneous devices with speeds rivaling wired connections, making WLANs the default for most homes and many offices.
Campus Area Network (CAN)
A CAN links multiple LANs across a campus — a university, a hospital complex, or a corporate park. It covers more ground than a single LAN but stays within a defined geographic boundary. CANs are typically owned and managed by the organization that uses them.
Metropolitan Area Network (MAN)
A metropolitan area network spans a city or metro region, typically covering 5 to 50 kilometers. MANs connect multiple LANs across different locations using fiber optic cables. City governments, universities with multiple campuses, and large companies with offices across a metro area are common MAN operators.
Wide Area Network (WAN)
A wide area network covers the largest geographic distances — cities, countries, or the entire globe. The internet itself is the world's largest WAN. WANs use satellite links, undersea cables, and leased lines to connect smaller networks across vast distances. Speed and cost vary widely depending on the infrastructure involved.
Network Components
Every network, regardless of size, is built from two categories of components: hardware and software.
Hardware
- Routers: Connect different networks and determine the best path for data. Your home router connects your LAN to your ISP and, through them, to the internet.
- Switches: Direct traffic between devices on the same network. Most home routers have a built-in switch.
- Access points: Provide wireless connectivity, allowing devices to join the network without cables.
- Cables: Ethernet (copper) for short distances, fiber optic for longer runs and higher bandwidth. The physical medium determines maximum speed and distance.
- Servers: Computers that provide services to other devices — file storage, email, web hosting, databases, and more.
Software
- Network Operating System (NOS): Manages connections, resource sharing, and communication between devices. Without it, hardware has no instructions for how to cooperate.
- Communication protocols: The rule sets (TCP/IP, DNS, DHCP, and others) that govern how data is formatted, transmitted, received, and acknowledged.
Essential Network Protocols
Protocols are what make interoperability possible. They are developed and maintained by standards organizations like the IETF, IEEE, and ISO. Here are the most important ones:
- TCP/IP (Transmission Control Protocol / Internet Protocol): The foundational protocol suite of the internet. IP handles addressing and routing; TCP ensures reliable, ordered delivery.
- DNS (Domain Name System): Translates human-readable domain names into IP addresses so your browser knows where to send requests.
- DHCP (Dynamic Host Configuration Protocol): Automatically assigns IP addresses to devices joining a network, eliminating manual configuration.
- HTTP/HTTPS (Hypertext Transfer Protocol): Used by web browsers to request and receive web pages. HTTPS adds encryption via TLS for security.
- UDP (User Datagram Protocol): A faster, simpler alternative to TCP that sacrifices reliability for speed. Used in video calls, live streaming, and gaming where real-time performance matters more than perfect delivery.
- FTP (File Transfer Protocol): Used for uploading and downloading files between computers over a network.
- SMTP (Simple Mail Transfer Protocol): Handles sending email between servers.
- ARP (Address Resolution Protocol): Maps IP addresses to MAC addresses within a local network so devices can find each other at the hardware level.
- ICMP (Internet Control Message Protocol): Used by diagnostic tools like ping and traceroute to test connectivity and identify routing problems.
The OSI Model
The OSI (Open Systems Interconnection) model is a framework that breaks network communication into seven layers. Each layer handles a specific part of the process. While modern networks primarily use the TCP/IP model, the OSI model remains essential for understanding and troubleshooting network problems because it clarifies exactly where an issue is occurring.
The seven layers, from bottom to top:
- Physical: Raw bit transmission over physical media — cables, radio waves, light pulses.
- Data Link: Device-to-device communication within a local network segment. Handles MAC addressing and error detection.
- Network: Packet routing between networks. This is where IP addressing operates.
- Transport: End-to-end delivery reliability (TCP) or speed (UDP).
- Session: Manages and maintains communication sessions between applications.
- Presentation: Data translation, compression, and encryption.
- Application: The layer users interact with directly — web browsers, email clients, file transfer tools.
Network Topologies
A network topology describes how devices are physically or logically arranged and connected. The topology you choose affects performance, fault tolerance, and cost. The most common topologies are:
- Point-to-point: The simplest topology — a direct connection between exactly two devices. No routing decisions needed.
- Star: All devices connect to a central hub or switch. Easy to manage and troubleshoot, but the hub is a single point of failure. Most home and small office networks use this topology.
- Ring: Devices connect in a circle, with data traveling in one direction around the loop. If one device fails, it can disrupt the entire ring unless redundancy is built in.
- Tree: A hierarchical structure that branches out from a central root — essentially star topologies connected together. Scales well but depends heavily on the root connection.
- Mesh: Every device connects directly to every other device. Highly reliable because data can take multiple paths, but complex and expensive to implement at scale.
- Hybrid: Combines elements of multiple topologies to balance flexibility, performance, and cost. Most real-world enterprise networks are hybrids.
IP Addresses and Networks
Every device on a network needs an address so other devices know where to send data. On IP networks, this address is the IP address. There are two versions in use today: IPv4 and IPv6.
Within a private network, devices use private IP addresses assigned by the router via DHCP. When traffic leaves the network for the internet, Network Address Translation (NAT) maps those private addresses to a single public IP — the one that websites and services see. You can check yours with our IP lookup tool.
Tools like VPNs and proxy servers can change the public IP address that others see, adding a layer of privacy to your network traffic.
Benefits of Computer Networks
- Resource sharing: Devices on the same network can share printers, storage, internet connections, and applications, reducing cost and duplication.
- Communication: Email, messaging, video conferencing, and file sharing all rely on network connectivity.
- Centralized data management: Servers can store data in one location, making backups simpler and access control easier to enforce.
- Scalability: Networks can grow by adding devices, switches, or additional network segments without rebuilding from scratch.
- Remote access: Users can connect to work resources from anywhere with an internet connection, enabling flexible and distributed work.
Network Security
Any connected network is a potential target. The same connectivity that makes networks useful also creates attack surface. Defending a network requires multiple layers of protection:
- Firewalls: Filter incoming and outgoing traffic based on security rules, blocking unauthorized access while allowing legitimate communication.
- Encryption: Scrambles data so that even if intercepted, it cannot be read without the decryption key. VPNs use encryption to protect data in transit.
- VPNs: Create encrypted tunnels between devices and networks, protecting data even on untrusted public networks.
- Authentication: Passwords, multi-factor authentication, and single sign-on (SSO) verify that only authorized users access network resources.
- Network monitoring: Continuous surveillance of network traffic helps detect unusual patterns that may indicate an intrusion or compromised device.
Malware and viruses can spread across networked devices. A single compromised machine can infect others on the same network. Strong security practices — keeping software updated, using strong passwords, and segmenting networks — protect everyone connected.
Useful Diagnostic Tools
Understanding networking concepts becomes practical when you can test and verify network behavior yourself:
- IP Lookup — see your public IP address, ISP, and approximate location.
- DNS Lookup — query A, AAAA, MX, TXT, and other DNS records for any domain.
- ASN Lookup — identify which network operator announces a given IP range.
- Reverse DNS — find the hostname configured for an IP address.
- WHOIS / RDAP — look up registration and ownership data for domains and IP ranges.
- Hostname to IP — resolve a domain name to its IP addresses.
- MAC Address Lookup — decode the hardware vendor from a network interface identifier.